Day 2 (Part 1) - User Entity, Password Encoder , BcryptPasswordEncoder
Olaoluwa Oke| 14 June 2023
I think I must’ve skipped over the User entity in my earlier notes.
That’s probably because I wrote it on Day One — fast. Mostly because
I had already written something nearly identical
for my bookmarking app, Tabitha.The style carried over nicely. And with the ERD already sketched out, this really wasn’t uncharted territory.
The model is intentionally plain: identity, contact, auth, membership, lifecycle.
Auth is next on the runway, so I wanted the substrate ready: stable fields, predictable lookups, and password handling that won’t make future-me wince.
The User entity is pretty standard:
Technical Log
(1) Domain Model
id
firstName
email
password
roomid
role
joinedAt
isActive
enum class Role { OWNER, MEMBER }
2. Repository Layer
interface UserRepository : MongoRepository<%User, String> {
fun findByEmailIgnoreCase(email: String): User?
fun findByRoomId(roomId: String): List<%User>
}
(3) Password Handling (BCrypt)
matches(raw: String, hash: String): Boolean
Rationale :
(4) DTOs (Auth-Adjacent)
Principles
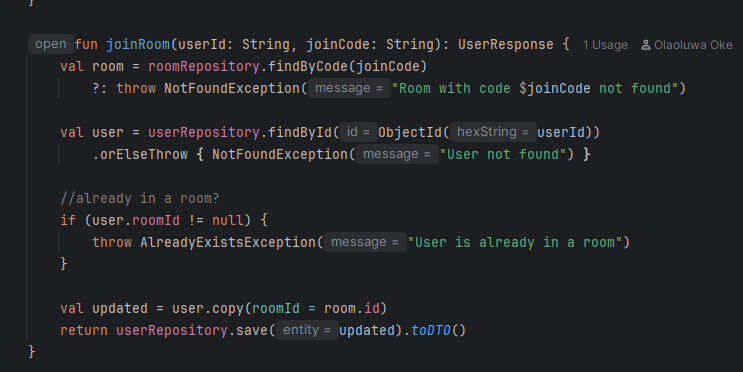
(5) Service Layer (UserService)
Injected deps: UserRepository, RoomRepository (see note below).Uses userRepository.findByRoomId(room.id) to determine role.
Why inject RoomRepository here?
(6) Validation & Errors
(7) Security Posture (pre-auth)